this article outlines how to evaluate network capabilities from both technical and operational dimensions when purchasing a cheap vps in malaysia: including how to look at bandwidth parameters, how to judge whether ddos protection is reliable, what testing methods are available, and what factors should be prioritized for different businesses to help you maximize availability and performance within a limited budget.
how much bandwidth is enough?
to evaluate bandwidth, you must first distinguish between peak bandwidth (peak gbps/mbps), guaranteed bandwidth (guaranteed bandwidth), and monthly traffic (gb/tb). simple websites or lightweight apis usually have 1–5mbps, but scenarios with many concurrent users or videos/large files need to be calculated based on concurrency: number of concurrencies × average rate per user ≈ required bandwidth. in addition, it depends on whether it is in "burst" mode and whether there is 95th percentile billing, which will affect peak traffic charges.
which bandwidth metric is the most critical?
key indicators include port speed (such as 1gbps port), guaranteed bandwidth, whether uplink and downlink are symmetrical, and monthly traffic limit. for delay-sensitive services, attention should also be paid to the network topology (number of hops to the local backbone), peering quality, and local isp connection. a common problem with cheaper solutions is high contention ratio, which can seriously affect the experience during peak periods.
how to evaluate ddos protection capabilities?
good ddos protection is not just about "protection", but depends on the protection capacity (gbps), the number and geographical distribution of cleaning centers, whether it supports l3/l4 and l7 layer cleaning, automatic detection and response time, and whether it provides bgp black holes, traffic mirroring or the ability to forward to cleaning channels. the tolerable attack peak promised by the supplier is as important as the actual sla and work order response time.
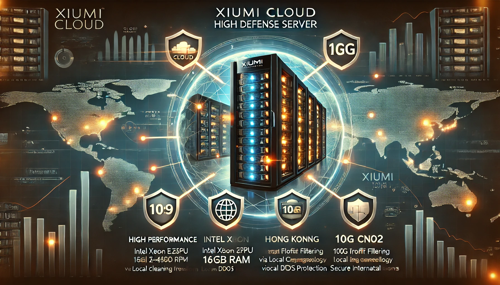
where can i find a cheap vps malaysia with good value for money?
when searching, give priority to local and regional service providers (kuala lumpur/penang data center), and also consider the nodes of international manufacturers in malaysian computer rooms. when comparing, check the network topology, upstream operators (such as whether it is directly connected to the main telco), and whether ddos cleaning is self-operated or outsourced by a third party. forums, reviews, and traceroute tools can help you identify real paths and delays.
why is it important to focus on both bandwidth and protection?
focusing only on bandwidth will ignore availability when attacks occur: even if the port is large, attack traffic can still exhaust host or link resources without effective cleaning; conversely, focusing on protection but with small bandwidth bottlenecks will cause congestion during normal traffic peaks. the combination of the two can ensure stable access and business continuity, especially for e-commerce, games or real-time communication services.
how to conduct actual testing and monitoring of suppliers?
actual measurement methods include: using iperf/iperf3 to measure the throughput of the target vps, conducting concurrent connection tests at different time periods, using speedtest or self-built scripts to measure latency and jitter; for ddos protection, you can ask about test simulation (small scale) or view historical attack mitigation cases and traffic cleaning delays. in the long term, prometheus/netdata, etc. are used to monitor bandwidth usage, packet loss, number of connections, and abnormal sudden increase alarms.
which solution is suitable for different types of businesses?
light blogs/small sites should give priority to vpss with on-demand bandwidth, low prices, and basic traffic limits; small and medium-sized e-commerce and api services should choose guaranteed bandwidth and scalable ports, and require basic l3/l4 protection; game servers and high-concurrency applications require low latency, large port rates, regional peering, and strong l7 cleaning capabilities. if the budget is limited, priority can be given to ensuring protection strategies and quick response mechanisms.
- Latest articles
- Network Design And Fault Recovery Strategy Using Malaysian Cn2 To Build A High-availability Architecture
- How Can Newbies Complete Taiwan Vps Server Rental And Resource Planning Within A Budget?
- How Overseas Users Use Japanese Native Ip L2tp To Access Local Services And Optimization Suggestions
- Stability Analysis Of Singtel's Computer Room Cn2 In Voip And Live Video Scenarios
- Best Practices For Using American Computer Room Servers In Enterprise-level Application Scenarios
- From The Perspective Of Security Operation And Maintenance, The Emergency Response And Recovery Process Of Japanese Server Cracking Software
- Technical Capabilities And Deployment Efficiency Analysis Of Common Technical Advantages Of High-quality Vietnamese Server Shops
- How To Judge Whether The Japanese Cn2 Gia Line Is Suitable For Your Website Access Needs
- Alibaba Cloud Malaysia Lightweight Server Entry-level Deployment And Performance Optimization One-step Tutorial
- How The Technical Team Tested The Bandwidth And Stability Of The Native Ip Of The Vietnam Server
- Popular tags
-
From Latency To Throughput, Malaysia Vps Evaluation Results Are Clear At A Glance
answers to five frequently asked questions about latency and throughput of vps in malaysia, including test methods, typical values, influencing factors and purchase optimization suggestions, to help you understand vps performance at a glance. -
Advantages And Usage Scenarios Of Choosing A Malaysian Traffic Card Vps
discuss the advantages and practical application scenarios of choosing malaysian traffic card vps to help users understand its importance. -
The Best Time And Precautions For Trying Out Malaysia Vps
this article details the best time and related precautions for trying out malaysia vps, and provides specific steps and operating guides.